Texas is on the brink of forcing Apple and Google to overhaul app downloads with strict age verification laws—are tech giants ready, or is your privacy about to get caught in the crossfire?
- The EU aborted their Chat Control vote knowing it would fail.
- Salesforce says it's not going to pay; customer data is released.
- Hackers claim Discord breach netted 70,000 government IDs.
- Microsoft to move Github to Azure. What could possibly go wrong.
- New California law allows universal data sharing opt-out.
- OpenAI reports that it's blocking foreign abuse. Who cares.
- IE Mode refuses to die, so Microsoft is burying it deeper.
- The massive mess created by Texas legislation SB2420.
- The BreachForums website gets a makeover.
- 100,000 strong global botnet attacking U.S. RDP services.
- UI experts weigh in on Apple's iOS 26 user-interface.
- 330,000 publicly exposed REDIS servers are RCE-vulnerable
Show Notes - https://www.grc.com/sn/SN-1047-Notes.pdf
Hosts: Steve Gibson and Leo Laporte
Download or subscribe to Security Now at https://twit.tv/shows/security-now.
You can submit a question to Security Now at the GRC Feedback Page.
For 16kbps versions, transcripts, and notes (including fixes), visit Steve's site: grc.com, also the home of the best disk maintenance and recovery utility ever written Spinrite 6.
Join Club TWiT for Ad-Free Podcasts!
Support what you love and get ad-free shows, a members-only Discord, and behind-the-scenes access. Join today: https://twit.tv/clubtwit
Sponsors:
[00:00:00] It's time for Security Now. Steve Gibson is here with good news on the EU chat control vote. We'll talk about that discord breach. Salesforce says we're not going to pay. And then there is a very bad bug in 330,000 publicly exposed Redis servers. It's got a CVSS of 10. Stay tuned. All will be revealed next on Security Now.
[00:00:29] Podcasts you love. From people you trust. This is TWiT. This is Security Now with Steve Gibson. Episode 1047. Recorded Tuesday, October 14th, 2025. Redis shells CVSS 10.0. It's time for Security Now. The show we cover the latest in security, privacy, computing, pretty much anything Steve Gibson wants to talk about because he's a
[00:01:01] the man of the hour. Hello, Mr. G. And I do try to largely keep us on topic as much as possible. Steve Gibson No, I'm the one who distracts. I'm the distractor. Steve Gibson There are there are there are sometimes we wander a little bit off the range, but I always get feedback from our listeners saying, hey, that was fun or that was interesting or like with, you know, like sci fi stuff. Steve Gibson Some of the best sci fi series that I've read have come from listeners saying, hey, that's true. Steve Gibson That's true.
[00:01:31] Steve Gibson Also some of the worst, but that's just the nature of that's just the nature of the game. Steve Gibson So that the topic I chose for today is is just one of a bunch of interesting news that we're going to cover.
[00:01:49] Steve Gibson And you know, it came at the end. So, okay, that's what we're going to talk about when we wrap things up. And that's a a arguably really worrisome remote code execution exploit in all Redis servers, which have been around for the last. Steve Gibson We use Redis. We use Redis for caching our website.
[00:02:20] Steve Gibson I do even yeah, even I have a Redis server at GRC. So anyway, it's got the it has earned itself the difficult to obtain 10.0 CVSS score.
[00:02:37] Steve Gibson And we're going to finish by talking about that. But we've got news on the EU's chat control vote, which we know is happening on the 14th of October, which is today for episode 1047 of security. Now Salesforce says it's not going to pay any ransoms and we're starting to see data leakage.
[00:03:04] Steve Gibson Hackers claim that discord lost control of 10s of 1000s of government IDs. We'll look at that. Steve Gibson Microsoft plans to move GitHub to Azure, which is where we roll out our what could possibly go wrong with that. Steve Gibson Actually, they tried a few times and then aborted the effort because it's not going to be easy.
[00:03:28] Steve Gibson We've got a new California law that our our governor Gavin Newsom signed last week that should be should help things. Steve Gibson We'll talk about that. Open AI blocking foreign abuse. Does anyone care? Steve Gibson There's actually some some news about about IE mode, which believe it or not, refuses to die.
[00:03:53] Steve Gibson We've got OK, we're going to spend a little bit of time on Texas law that's going into effect on January 1st. Tim Cook reportedly phoned Greg Abbott and said, please, please don't let this happen. Veto this or at least amend it because it's really bad. Well, Greg, you know, I don't think he has much sympathy for anything. Tim Cook has to say. So we're getting this in 10 weeks.
[00:04:22] And oh, boy, is it going to be a problem? Also, Breach Forum, which I we showed last week, the Breach Forums Web page. Remember, that was with the extortion demand from Salesforce. Well, that site has received a makeover, which we'll be looking at today.
[00:04:42] Also, we've got a oh, boy, a 100000 strong global botnet attacking U.S.-based RDP services. And again, what could possibly go wrong there? I did see one of our listeners sent me a UI experts weigh in on Apple's iOS 26 user interface. I did talk a little bit about going off topic.
[00:05:10] Well, I just have to indulge myself here. You don't like it one bit. I know. Oh, it turns out I'm in good company. Yeah. Yes. Anyway, so that the Redis servers, we got a picture of the week. And I think maybe, Leo, this time we've got a good podcast. For once. Yeah, I think it's about damn time. Maybe this will be worthwhile.
[00:05:37] I should mention, this is also the last patch Tuesday for Windows 10. Today. That's right. End of life. Ho, ho, ho. Ho, ho, ho. For Windows 10. Ho, ho, ho. Except, of course, if you click your heels twice and look at the moon, then Microsoft says, okay, fine. I, well, before we get to the picture of the week, because I know that's imminent.
[00:06:05] And I have not, as always, I have preserved. I've stayed all week in a soundproof room and I've preserved my integrity. Are you going to tell our listeners who's paying the bills? I'm going to tell our listeners who's paying the bills. Exactly. This portion of security now brought to you by Zscaler, the world's largest cloud security platform. The world's largest, let me say that again, cloud security platform. Pretty good.
[00:06:34] As organizations leverage AI to grow their business and support workforce productivity, they can't rely anymore on traditional, you know, network-centric security solutions, perimeter defenses that just don't protect against emerging threats and particularly against AI attacks. Bad actors have jumped on AI like everybody else, like business too, right? AI is amazing. They're using new AI capabilities and powerful AI agents.
[00:07:01] And they're using it across all four attack phases, which I think is interesting. They're using AI to discover the attack surface, to compromise it. Once in, they're using AI to move laterally. They're using AI to exfiltrate data. That's what Salesforce is learning about right now. Traditional firewalls and VPNs, in fact, don't help. Instead, they expand your attack surface by giving you public IP addresses. They enable lateral threat movement.
[00:07:30] They're also more easily exploited with AI-powered attacks. So what do we need? We need a more modern approach. We need, say it with me, Z-scalers, zero trust plus AI that A, removes your attack surface, B, secures your data everywhere, and very importantly, C, safeguards your use of public and private AI.
[00:07:55] And then finally, of course, the most important, protects against ransomware and AI-powered phishing attacks. Just think about the job Steve Harrison has to do. He is the CISO of MGM Resorts International. They've been hit in the past. They're not taking any chances. They chose Z-scaler. He says, with Z-scaler, quote, we hit zero trust segmentation across our entire workforce in record time.
[00:08:23] And the day-to-day maintenance of the solution with data loss protection, with insights into our applications, these were really quick and easy wins from our perspective. Here's a guy who knows the risks and has chosen Z-scaler to protect his entire organization. With zero trust plus AI, you could thrive in the AI era. You could stay ahead of competition. And you can remain resilient even as threats and risks evolve.
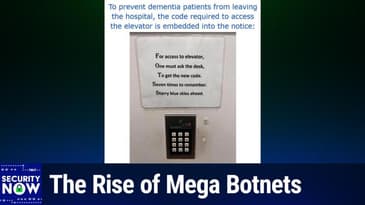
[00:08:51] Learn more at zscaler.com slash security. Zscaler.com slash security. We thank them so much for their support of security now. And now I shall turn on my extra camera so that we can see. This was just a picture. This was very clever. The goal is to prevent dementia patients from leaving the hospital, which has an elevator. Okay.
[00:09:21] My mom is in a memory care ward and that's exactly right. They have a code panel in the elevator. Right. Right. And so above this code, it says for access to elevator, one must ask the desk to get the new code seven times to remember starry blue skies ahead. Whoa, that's a code is four, one, two, seven.
[00:09:50] The first word of the first four sentences. And they've capitalized each of them too, to make it a little bit more obvious. But if you've got dementia, you're probably not going to be able to. Uh-huh. Yeah. Well, no, no one would tell you. So, right. So here is the code published above the keypad for access to elevator. One must ask the desk to get the new code seven times to remember.
[00:10:20] And so four, one, two, seven. So everybody who all of the staff. This is kind of brilliant. Isn't it wonderful? Yeah. Yeah. And nobody would ever think, they would think, oh, I better go to the desk and ask for the new code. You know what? I'm stupid enough. That's exactly what I would have done. Oh, that's clever. I like it. I like it. Yeah. In order to get up to see my mom, I have to get them to come and open the door and enter the code and bring me up.
[00:10:48] And then I have to do the same to get down. And I wish they had something like this, but they don't. I have to help every time. That's all right. Yeah. Okay. So the much anticipated. Yes. Good news. The much anticipated vote among EU member countries originally slated for today, October 14th, was called off.
[00:11:13] Once it became clear that the vote for the adoption of the controversial measure would fail. Thankfully. Remember, last week we reported that Germany seemed to be waffling a little bit, although the Netherlands said they were a firm no. Turns out Germany made up their mind also signaling a firm no. I learned of this from a blurb on the Risky Business newsletter, which offered some additional detail.
[00:11:40] They wrote, the European Union has scrapped the vote on chat control, proposed legislation that would have mandated tech companies to break their encryption to scan content for child abuse materials. The project was supposed to be put to a vote on Tuesday, October 14th, during a meeting of interior ministers of EU member states. Denmark, which currently holds the EU presidency and was backing the legislation, scrapped the
[00:12:08] vote, according to reports on Austrian and German media. Danish officials scrapped the vote after failing to gather the necessary votes to pass the legislation and advance it to the EU parliament. Only 12 of the bloc's 27 members publicly backed the proposal, with nine against and the rest undecided. The final blow to chat control came over the past two weeks when both the Netherlands and Germany publicly opposed it.
[00:12:42] Germany's justice minister, Dr. Stephanie Hubig, went out of her way to describe chat control as a, quote, taboo for the rule of law, unquote, arguing that the fight against child pornography does not justify removing everyone's right to privacy. She used the phrase suspicionless chat control. And I think that's key because, of course, it was for everyone, not just. That's really. Yes. Yeah. Yeah. Right.
[00:13:13] Well, I mean, and that's what you have to do. If you're going to find people you don't know, it's going to scan everybody sharing illegal content. Everybody has exactly. It's like if a website says you have to be an adult. Well, then everybody has to prove their age, you know, not just young people because you don't know. So anyway, the risky business newsletter said the law has been seen, has seen the usual mass
[00:13:41] opposition from privacy groups such as the EFF, but also from the tech sector, too, with over 40, four zero major EU tech companies signing an open letter to EU officials. Signatories describe chat control as and this is really interesting. I'm going to share this letter because it also contains some interesting stuff.
[00:14:05] They quote, quote, a blessing for U.S. and Chinese companies, unquote, since EU users will migrate to products that respect their privacy and ignore chat control. The chat control opposition also received major help from a Danish programmer whose fight chat control website allowed Europeans to mass mail their representatives and urged them to vote
[00:14:35] against. According to a political Europe report, the website had driven so much traffic that it broke the inboxes of EU members of parliament over the past few weeks. And you can imagine that might get their attention. So, you know, it's one thing to be living within a government that declares itself to be a democracy, but it's truly wonderful to see a movement where the voices, opinions and feelings of that democracy's
[00:15:04] subjects can be and are heard. So I checked out that open letter, as I mentioned, to the EU parliament that was signed by 40 major European union companies. Since this is one of the major issues of our time, I want to share that letter. It was addressed to open letter to EU member states on their proposed CSA regulation. And it read, dear minutes.
[00:15:28] So this is from the 40, you know, co-signed by the 40 top tech companies in the EU, dear ministers and ambassadors of EU member states. We, the undersigned European enterprises, as well as the European digital SME alliance, you know, small, medium enterprise alliance, which represents more than 45,000 digital, small
[00:15:54] and medium enterprises across Europe, write to you with deep concern regarding the proposed regulation on child sexual abuse. Protecting children and ensuring that everyone is safe on our services and on the Internet in general is at the core of our mission as privacy focused companies. We see privacy as a fundamental right, one that underpins trust, security and freedom online
[00:16:22] for adults and children alike. However, we are convinced that the current approach followed by the Danish presidency would not only make the Internet less safe for everyone, but also undermine one of the EU's most important strategic goals, progressing toward higher levels of digital sovereignty. Digital sovereignty is Europe's strategic future.
[00:16:50] In an increasingly unstable world, Europe needs to be able to develop and control its own secure digital infrastructure, services and technologies in line with European values. The only way to mitigate these risks is to empower innovative European technology providers. Digital sovereignty matters for two key reasons. First, economic independence.
[00:17:19] Europe's digital future depends on the competitiveness of its own businesses. But forcing European services to undermine their security standards by scanning all messages, even encrypted ones, using client-side scanning would undermine users' safety online and go against Europe's high data protection standards.
[00:17:45] Therefore, European users, individuals and business alike, and global customers will lose trust in our services and turn to foreign providers. This will make Europe even more dependent on American and Chinese tech giants that currently do not respect our rules, undermining the bloc's ability to compete. And second, national security. And second, national security. Encryption is essential for national security.
[00:18:14] Mandating what would essentially amount to backdoors or other scanning technologies inevitably creates vulnerabilities that can and will be exploited by hostile state actors and criminals. For this exact reason, governments exempted themselves from the proposed CSA scanning obligations.
[00:18:36] Nevertheless, a lot of sensitive information from businesses, politicians and citizens will be at risk should the CSA regulation move forward. It will weaken Europe's ability to protect its critical infrastructure, its companies and its people. The CSA regulation will undermine trust in European businesses. Trust is Europe's competitive advantage.
[00:19:04] Thanks to the GDPR and Europe's strong data protection framework, European companies have built services that users worldwide rely on for data protection, security and integrity. This reputation is hard earned and gives European-based services a unique selling point which big tech monopolies will never be able to match.
[00:19:28] This is one of the few, if not the only, competitive advantage Europe has over the U.S. and China in the tech sector. But the CSA regulation risks reversing this success. This legal text would undermine European ethical and privacy-first services by forcing them to weaken the very security guarantees that differentiate European businesses internationally.
[00:19:57] This is particularly problematic in a context where the U.S. administration explicitly forbids its companies to weaken encryption, even if mandated to do so by EU law. Ultimately, the CSA regulation will be a blessing for U.S. and Chinese companies as it will make Europe kill its only competitive advantage and open even wider the doors to big tech.
[00:20:26] The EU has committed itself to strengthening cybersecurity through measures such as NIS-2, the Cyber Resilience Act and the Cyber Security Act. These policies recognize encryption as essential to Europe's digital independence. The CSA regulation, however, must not undermine these advancements by effectively mandating systemic vulnerabilities.
[00:20:50] It is incoherent for Europe to invest in cybersecurity with one hand while legislating against it with the other. European small and medium-sized enterprises, SMEs, would be hit hardest if obliged to implement client-side scanning.
[00:21:10] Unlike large technology corporations, SMEs often do not have the financial and technical resources to develop and maintain intrusive surveillance mechanisms, meaning compliance would impose prohibitive costs or force market exit.
[00:21:27] Moreover, many SMEs build their unique market position on offering the highest levels of data protection and privacy, which particularly in Europe is a decisive factor for many to choose their products over the counterparts of big tech. Mandating client-side scanning would undermine this core value proposition for many European companies.
[00:21:51] This will suffocate European innovation and cement the dominance of foreign providers. Instead of building a vibrant, independent digital ecosystem, Europe risks legislating its own companies out of the market.
[00:22:07] For these reasons, we call on you to reject measures that would force the implementation of client-side scanning, backdoors, or mass surveillance of private communications, such as we currently see in the Danish proposal for a council position on the CSA regulation. Second, protect encryption to strengthen European cybersecurity and digital sovereignty.
[00:22:35] Third, preserve the trust that European businesses have built internationally. Fourth, ensure that EU regulation strengthens rather than undermines the competitiveness of European SMEs. And pursue child protection measures that are effective, proportionate, and compatible with Europe's strategic goal of digital sovereignty.
[00:23:02] Digital sovereignty, they finish, cannot be achieved if Europe undermines the security and integrity of its own businesses by mandating client-side scanning or other similar tools or methodologies designed to scan encrypted environments, which technologists have once again confirmed cannot be done without weakening or undermining encryption.
[00:23:26] To lead in the global digital economy, the EU must protect privacy, trust, and encryption. So that's sort of the business side, you know, business-centric view of what this meant for the EU's businesses. And I wanted to share that because we don't want this to rear its ugly head again.
[00:23:53] You know, I mean, it's hard to put this thing to bed once and for all. We keep, you know, smacking it down and it pops up because, you know, legislators say, well, but what about the children? And that gets everybody all riled up again. So hopefully this is, you know, having this come to as much ahead as it has and really getting everyone's attention, notice that they weren't breaking encryption.
[00:24:20] They figured out, okay, we're not going to do that. We're going to do client-side scanning before and after encryption, believe that alone, you know, trying to come up with a way of shimming their scanning into the system. And even that didn't go. The idea being, no, sorry, we're just not, we're not going to become a surveillance state.
[00:24:43] Doing that would, you know, we're thinking of companies like Threema, right, that are EU-based and couldn't do what they do. I mean, it would just kill the Threema messenger completely to have to operate under a chat control legislation. So one line stood out for me in that letter that I thought was interesting.
[00:25:11] It said, this is particularly problematic in a context where the U.S. administration explicitly forbids its companies to weaken encryption, even if mandated to do so by EU law.
[00:25:27] Even though it wasn't the EU, you know, that feels like a response to the U.K.'s order, right, to Apple, which, as we know, was loudly and publicly rebuffed when Tulsi Gabbard, the U.S. director of national intelligence, tweeted on X that as a result of the U.S. administration's closely working with the U.K.,
[00:25:50] Americans' private data would remain private and our constitutional rights and civil liberties would be protected. You know, she stated in that tweet that, quote, as a result, the U.K. has agreed to drop its mandate for Apple to provide a backdoor that would have enabled access to the protected encrypted data of American citizens and encroached on our civil liberties, unquote.
[00:26:18] So, you know, unfortunately, as we know, it's now believed that the U.K. has since issued another order to Apple requiring it to allow the government access to the iCloud data of its own citizens. Not everyone everywhere. And so we're going to see how that plays out.
[00:26:36] Overall, though, I think that this open letter made a very good point about the fundamental competitive disadvantage that the entire EU business sector would face if its companies were forced to abide by a clearly, you know, surveillance-oriented privacy-invading law. They're right about, you know, what the rest of the world would do in response. So anyway, that bullet got dodged.
[00:27:06] You know, we still have this unknown order in the U.K. And of course, the U.K. is still strong on enforcing age restrictions. So we're going to see how those things continue to play out. Yeah, you saw, well, probably going to talk about it, but you saw what California did with that. Yeah. Yeah. Yeah. Okay. So Salesforce said, uh-uh, it's not going to pay.
[00:27:36] And this is the extortion demand threatening a billion. Actually, it was 984 million, you know, just shy of a billion records belonging to, it's believed to be 39 of its customers whose networks were all breached as a consequence of their relationship with Salesforce.
[00:27:59] So, as I said, last week we showed the ransom demand posted to breach forums by the scattered lapses hunters group. Salesforce public response was widely covered in the tech press. Here's what Dan Gooden writing for Ars Technica said.
[00:28:17] He wrote, Salesforce says, it's refusing to pay an extortion demand made by a crime syndicate that claims to have stolen roughly 1 billion records from dozens of Salesforce customers. Google's Mandiant group said in June that the threat group making the demands began their campaign in May when they made voice calls to organizations storing data on the Salesforce platform.
[00:28:45] The English-speaking callers would provide a pretense that necessitated the target connect an attacker-controlled app. We know that now that that was an OAuth-based authentication app to their Salesforce portal. Dan wrote, amazingly, but not surprisingly, many of the people who received the calls complied.
[00:29:09] The threat group behind the campaign is calling itself Scattered Lapsus Hunters, a mashup of three prolific data extortion actors, Scattered Spider, Lapsus, and Shiny Hunters. Mandiant, meanwhile, tracks the group as UNC 6040 because the researchers so far have been unable to positively identify the connections.
[00:29:33] Earlier this month, the group created a website that named Toyota, FedEx, and 37 other Salesforce customers whose data was stolen in the campaign. In all, the number of records recovered Scattered Lapsus Hunters claimed was, oh, it's 989.45 million, approximately a billion.
[00:29:57] The site called on Salesforce to begin negotiations for a ransom amount, quote, or all your customers' data will be leaked, unquote. The site went on to say, nobody else will have to pay us if you pay, Salesforce Inc. The site said the deadline for payment was last Friday. In an email Wednesday, a Salesforce representative said the company is spurning the demand.
[00:30:24] The representative wrote, quote, I can confirm Salesforce will not engage, negotiate with, or pay any extortion demand. The confirmation came a day after Bloomberg reported that Salesforce told customers in an email that it won't pay the ransom. The email went on to say that Salesforce had received credible threat evidence
[00:30:48] indicating a group known as shiny hunters planned to publish data stolen in the series of attacks on customers' Salesforce portals. The refusal comes amid a continuing explosion in the number of ransomware attacks on organizations around the world.
[00:31:05] The reason these breaches keep occurring is the hefty sums the attackers receive in return for decrypting encrypted data and or promising not to publish stolen data online. Security firm DeepStrike estimated that global ransom payments totaled $813 million last year,
[00:31:31] that being down from $1.1 billion in 2023. So $1.1 billion in ransom payments in 2023, $813 million in 2024. Dan wrote, the group that breached drug distributor Sencora alone received a whopping $75 million in ransomware payments,
[00:32:00] Bloomberg reported, citing unnamed people familiar with the matter. So one payout of $75 million for the breached drug distributor Sencora's ransom payment. No wonder these guys, you know, stay at it. Making ransomware payments, he finishes, has come increasingly under fire by security experts who say the payments reward the bad actors responsible and only encourage them to pursue more riches. Right.
[00:32:29] Independent researcher Kevin Beaumont wrote on Mastodon, referring to the UK's National Crime Agency, quote, corporations should not be directly funding organized crime with the support of the National Crime Agency and their insurance. Break the cycle. Beaumont said in an interview, while the NCA publicly recommends against paying ransoms, multiple organizations he's talked to report having NCA members present during ransom negotiations.
[00:32:58] On Mastodon, Kevin warned that payments pose threats to broader security, writing, it's becoming a real mess to defend against this stuff in the trenches. Let me tell you, I'm concerned about where this is going, unquote. So I imagine that Kevin is worried because there's no end in sight.
[00:33:20] The bad guys have figured out that the human factor is reliably the weakest link in the enterprise security chain. This gets the attackers inside the enterprise and enterprise networks are not currently hardened against abuse from the inside. Among the approximately 39 companies believed to have been breached due to their customer relationship with Salesforce,
[00:33:47] Sales Loft and Drift is the Australian airline Qantas that we talked about last week with its loony injunction against anyone republishing their data after it's leaked on the dark web. Like those guys are going to care about an injunction. And also reportedly the Australian telco Telstra, although Telstra is denying the Cyber Daily report of their breach.
[00:34:11] Unfortunately, these ransomware groups are compelled to release the data they have obtained once they've made such a public spectacle of their data breach, right? You know, they can't ever be seen to be bluffing or making empty threats or they'll lose their ability to threaten.
[00:34:31] So I imagine that next week we'll be seeing stories of nearly 1 billion records of data from around 39 major Salesforce customers being leaked online. The bad guys need to leak the data so their next victim will take them seriously. Oh, Leo, what a world. But we have some good news and it comes from one of our sponsors.
[00:34:58] That I can definitely provide you with. Can't help you with the other stuff, though, unfortunately. That's unbelievable. I swear. We live in difficult times. And now we're after this, we're going to talk about the extent of Discord's horrible breach. Yeah. And of course, since we use Discord for our club, I read that story with great interest.
[00:35:23] I have never been asked for my government ID from Discord, but I asked in our club and a number of our club members have. Mostly outside the U.S. And it's when their estimate of your age needs to be challenged. So they come back and they say, we think you're a teenager. Yeah. And it's like, you know. You talk a lot about Pokemon Go. I don't know. Right. Yeah.
[00:35:51] Actually, we looked at your discourse on Discord and it looks a little junior. Yeah. There's no question. I'm a kid. We will get to that in just a bit. But first, a word from our sponsor, my favorite VPN. I'm talking, of course, about ExpressVPN. Let me just click this link so I can get the full screen and Steve can have a little privacy.
[00:36:21] We'll talk about protecting your privacy online, right? If you've ever browsed in incognito mode, well, you know, I think we've talked about it. It's probably not as incognito as you think. Google recently settled a $5 billion lawsuit with a B. Billion dollar lawsuits being accused of secretly tracking users in incognito mode. Google's defense is, well, incognito doesn't mean invisible. In fact, you're not.
[00:36:49] All of your online activity is still 100% visible to third parties. Don't use incognito mode. Use ExpressVPN, the only VPN I use and trust. And you better believe when I go online, especially when I'm traveling in airports or coffee shops or I'm outside the country, ExpressVPN is my go-to. Why does everyone need ExpressVPN? Well, with ExpressVPN, these third parties can still see every website you visit, even in incognito mode. Who are the third parties?
[00:37:19] Your internet service provider. They see what you're doing. Or your mobile network provider. Whoever administers that Wi-Fi network you're on, if it's at your school, the school IT department, if it's at work, your boss. ExpressVPN reroutes 100% of your traffic through secure encrypted servers. So third parties can't see your browsing history. They can't see whatever you're, they can't see anything. They just see gobbledygook. They see encrypted data. It works beautifully.
[00:37:49] Now, I should point out that when you do get to the ExpressVPN server, the end point of that encrypted tunnel, you have to be unencrypted, right? So you can browse. You can't maintain it. So it's really important you choose a VPN provider that protects your data because they're at the other end of that tunnel. That's why I use ExpressVPN. They make the extra effort to keep you private.
[00:38:18] ExpressVPN completely hides your IP address, which means it's very difficult for third parties to track your online activity. To them, you look like one of other, hundreds of other people using that same IP address, ExpressVPN customers. The other thing they do, though, that I think is really important, they rotate their IP addresses. They spend the extra money to make sure those IP addresses change. So it really is hard to track you. It's hard to even know that you're on a VPN, which is great. ExpressVPN is easy to use.
[00:38:47] You fire up the app, you click one button, you're done. You're protected. And it works everywhere on all devices, phones, laptops, tablets. Even you can put it on your router to protect your whole house. You can stay private on the go and at home, wherever you are. And ExpressVPN is rated number one by the top tech reviewers, people like CNET and The Verge. It's what I use. Secure your online data today by visiting expressvpn.com slash security now.
[00:39:15] That's E-X-P-R-E-S-S-V-P-N dot com slash security now. To find out how you can get up to four extra months, expressvpn.com slash security now. Expressvpn.com slash security now. We thank you so much for supporting security now. And Steve Gibson. Back to you, Stevie. So.
[00:39:41] Hackers are claiming that the Discord breach exposed the data of 5.5 million users. Ooh, I didn't know it was that many. Yeah. Ooh. Yeah. But not the government IDs. That's a subset. So, since my initial reporting of the Discord breach last week, additional troubling details have surfaced.
[00:40:06] Bleeping Computer reports this significant breach at Discord, though the attackers and Discord numbers don't agree. Bleeping Computer reported, Discord says they will not be paying threat actors who claim to have stolen the data of 5.5 million unique users from the company's Zendesk support system instance.
[00:40:29] The stolen data includes government IDs and partial payment information for some people. The company is also pushing back on claims that 2.1 million photos of government IDs were disclosed in the breach, stating that approximately, as if this is not, I mean, this is not much better, 70,000 users had their government ID photos exposed.
[00:40:59] So, folks, we need a better solution for proving age. Wow. This shows exactly why. Yeah. Yes. So, they said, while the attackers claimed the breach occurred through Discord's Zendesk support instance, the company has not confirmed this and only described it as involving a third-party service, so they're being coy, used for customer support. Gee, I wonder what that could be.
[00:41:24] Discord told Bleeping Computer in a statement, quote, first, as stated in our blog post, this was not a breach of Discord. Okay. Who cares? That's not a breach of Discord.
[00:42:04] Zero-day export may be attacked. Uh-huh. Which our vendor, they wrote, used to review age-related appeals. Third, we will not reward those responsible for their illegal actions. In a conversation, writes Bleeping Computer with the hackers, Bleeping Computer was told that Discord is not being transparent. So, Bleeping Computer talked to the hackers.
[00:42:31] And the hackers said, discord is not being transparent about the severity of the breach, stating that they stole 1.6 terabytes of data from the company's Zendesk instance. According to the threat actor, they gained access to Discord's Zendesk instance for 58 hours, beginning on, you know, because it takes a while to exfiltrate 1.6 terabytes of data. Yeah.
[00:43:00] It gained access for 58 hours, beginning on September 20th, 2025. However, the attackers say the breach did not stem from a vulnerability or breach of Zendesk, but rather from a compromised account belonging to a support agent employed through an outsourced business process outsourcing.
[00:43:23] That's our new term of art, a BPO, a BPO, business process outsourcing provider used by Discord. As many companies have outsourced their support and IT help desks to BPOs, they have become a popular target for attackers to gain access to downstream customer environments.
[00:43:44] The hackers allege that Discord's internal Zendesk instance gave them access to a support application known as ZenBar that allowed them to perform various support-related tasks, such as disabling multi-factor authentication and looking up users' phone numbers and email addresses.
[00:44:05] Using access to Discord support platform, the attackers claim to have stolen 1.6 terabytes of data, including around 1.5 terabytes of ticket attachments and over 100 gigabytes of ticket transcripts. The attackers say this consisted of roughly 8.4 million tickets, affecting 5.5 million unique users. I'll just mention that all those numbers track.
[00:44:34] They all make sense in terms of the ratios that you would expect to see. And that about 580,000 users contain some sort of payment information. The threat actors themselves acknowledge the belief in computer that they're unsure how many government IDs were stolen, but they believe it's more than 70,000. As they say, there were approximately 521,000 age verification tickets.
[00:45:04] So more than half a million age verification tickets among the 8.4 million tickets total.
[00:45:13] The threat actors also shared a sample of the stolen user data, which can include a wide variety of information, including email addresses, Discord usernames and IDs, phone numbers, partial payment information, date of births, multi-factor authentication-related information, suspicious activity levels, and other internal info.
[00:45:35] The payment information for some users was allegedly retrievable through Zendesk integrations with Discord's internal systems. These integrations reportedly allowed the attackers to perform millions of API queries to Discord's internal database via the Zendesk platform and retrieve further information.
[00:45:58] Bleeping computer could not independently verify the hackers' claims or the authenticity of the provided data samples. The hacker said the group demanded $5 million in ransom, only $5 million, later reducing it to $3.5 million, and engaged in a private negotiation with Discord between September 25th and October 2nd.
[00:46:22] After Discord ceased communications and released a public statement about the incident, the attacker said they were extremely angry and planned to leak the data publicly if an extortion demand is not paid. Bleeping computer contacted Discord with additional questions about these claims, including why they retained government IDs after completing age verification. That's the key. Yeah.
[00:47:20] Thanks to Bleeping computer's pursuit of this. This is what we are increasingly seeing. We are seeing that automated backend systems, which publish an API, are then being used by their clients or their customers in order to get the services. So, like Discord's platform accesses to Zendesk or vice versa.
[00:47:50] You know, they've got APIs going in both directions. Which means that if, and in this case, this BPO guy, this business process outsourced person, they got compromised. Who knows? Who knows? Clicked on email, phishing, whatever. That allowed their credential, which allowed them to log into either Discord or Zendesk to get them in.
[00:48:16] And then the bad guys were able to use basically the automated API cross-access in order to plumb the other services. Using the API at high speed in order to obtain more data and create problems.
[00:48:39] So, basically, what's happened is we've sort of that enterprises that are establishing operational backends have like an underground private network, which is data rich.
[00:48:59] And now bad guys are breaking into that and then taking advantage of these APIs in order to suck out all of the data that is normally, you know, layers deep from the front end that users see. You know, convenient for those people who are doing it. But, boy, it magnifies the effect of a breach when one happens. And guess what? They're happening.
[00:49:29] And, yeah, maybe half a million government IDs. And as you clued in on, as we mentioned before, why are the age verification records being kept? That's just lazy. That's just lazy. Well, and it's also, it's data aggregation fever. I mean, it's like, oh, the more data we have, you know, who knows what we'll be able to do with this in the future. Right.
[00:49:55] So, why delete what might be of some value to us? Yikes. Okay. So, I suppose it was only a matter of time. Before Microsoft would decide to move its GitHub property over to their own Azure cloud infrastructure. But the details behind the move will likely be of interest to many of our listeners.
[00:50:25] The publication, The Next Stack, provided the background for this move. They wrote,
[00:51:00] Now, according to internal GitHub documents the new stack has seen, the next step of this deeper integration into Microsoft's structure is moving all of GitHub's infrastructure to Azure, even at the cost of delaying work on new features.
[00:51:20] In a message to GitHub staff, CTO Vladimir Fedorov notes that GitHub is constrained on capacity in its Virginia data center. He writes, quote, it's existential for us to keep up with the demands of AI and co-pilot. Well, of course, Leo, you know, if you're going to have AI and co-pilot, you got to move to a facility that's big enough for that.
[00:51:47] He said, which are changing how people use GitHub. The plan, he writes, is for GitHub to completely move out of its own data centers in 24 months. Quote, this means we have 18 months to execute with a six month buffer. Fedorov memo says he acknowledges that since any migration of this scope will have run in parallel.
[00:52:15] On both the new and old infrastructure for at least six months, the team realistically needs to get this work done in the next 12 months. So during 2026. To do so, he's asking GitHub's teams to focus on moving to Azure over virtually everything else.
[00:52:39] Fedorov wrote, quote, we will be asking teams to delay feature work to focus on moving GitHub. We have a small opportunity window where we can delay feature work to focus and we need to make that window as short as possible, unquote. While GitHub had previously started work on migrating parts of its service to Azure, they write,
[00:53:03] our understanding is that these migrations have been halted, halting, and sometimes failed. There are some projects like its data residency initiative, internally referred to as Project Proxima, that will allow GitHub Enterprise users to store all of their code in Europe that already solely use Azure's local cloud regions. Fedorov writes, we have to do this.
[00:53:33] It's existential for GitHub to have the ability to scale to meet the demands of AI and Copilot, and Azure is our path forward. We have been incrementally using more Azure capacity in places like Actions, Search, Edge Sites, and Proxima, but the time has come to go all in on this move and finish it, unquote.
[00:54:01] The next stack said, GitHub has recently seen more outages in part because its central data center in Virginia is resource constrained and running into scaling issues. AI agents are part of the problem, but it's our understanding that some GitHub employees are concerned about this migration because GitHub's MySQL clusters, which form the backbone of the service and run on bare metal servers,
[00:54:31] won't easily make the move to Azure and lead to even more outages going forward. In a statement, a GitHub spokesperson confirmed our reporting and told us, quote, GitHub is migrating to Azure over the next 24 months because we believe it's the right move for our community and our teams.
[00:54:56] We need to scale faster to meet the explosive growth in developer activity and AI-powered workflows, and our current infrastructure is hitting its limits. We're prioritizing this work now because it unlocks everything else. For us, availability is job one, and this migration ensures GitHub remains the fast, reliable platform developers depend on
[00:55:22] while positioning us to build more, ship more, and scale without limits. This is about ensuring GitHub can grow with its community at the speed and scale the future demands. For open source developers, having GitHub linked even closer to Microsoft and Azure may also be a problem, though for the most part, some of the recent outages and rate limits developers have been facing
[00:55:51] have been the bigger issue for the service. Microsoft has long been a good steward of GitHub's fortunes, but in the end, no good service can escape the internal politics of a giant machine like Microsoft, where executives will always want to increase the size of their fiefdoms. So to me, it makes sense for Microsoft, but it also sounds as though it's going to be more easily said than done.
[00:56:20] And the thing about unforeseen consequences is that they're unforeseen, and outages for any service such as GitHub, upon which so much depends, are going to be a big problem. But no one sees another way. So I had the feeling that some future Security Now podcasts will be reporting on the consequences of this move. And boy,
[00:56:48] if like moving to Azure gets screwed up from a security standpoint, that's going to be a big nightmare for GitHub, because that's not something anyone wants to see happening. So I've been noting that the proper place for consumers to specify how they would like the internet to treat them is their browser. You know,
[00:57:18] that was what I love so much about the original DNT, that, you know, the do not track beacon with just the flip of a switch. Just once, a user could configure their web browser to always append a DNT header to every internet resource request. And had anyone ever cared to honor that request, which of course was the big problem,
[00:57:47] that would have been their one and done prohibition against tracking. Because this broad concept has merit. The newer incarnation of DNT is GPC, the global privacy control. And remember, globalprivacycontrol.org is a site you can go to, and right up at the top of the page,
[00:58:14] you are notified whether your browser is broadcasting the GPC signal saying, no thank you. But even though the GPC signal has been around since its release, for like quite a while, sorry, only today, only Brave, the DuckDuckGo,
[00:58:42] and Tor browsers are broadcasting that signal by default. Firefox, since its release number 95, has supported GPC, but it needs to be turned on. And of course, I went over to globalprivacycontrol.org with Firefox, and yep, right up at the top, I get a little green light saying, your browser is GPC enabled. Sadly, and perhaps not surprisingly,
[00:59:12] there's no support for GPC from the various other Chrome-based browsers. Chrome, Edge, Vivaldi, and Opera. Anyone wishing to emit the GPC signal from any Chromium-based browser other than Brave will need to install an add-on. And there's also been no sign of GPC from Safari, which I find kind of surprising. Okay, so, all that makes news, all of that makes news,
[00:59:43] is because of California's new legislation last Wednesday, which Gavin Newsom signed. The record reported, California Governor Gavin Newsom, on Wednesday, signed a bill, which requires, that's right, requires, web browsers, to make it easier for Californians, to opt out, of allowing third parties, to sell their data.
[01:00:12] The California Consumer Privacy Act, signed in 2018, gave Californians the right, to send opt-out signals, but major browsers, have not, had to make opt-outs, simple to use. The bill signed Wednesday, requires browsers, to set up, an easy to find mechanism, that lets Californians, opt out, with the push of a button, instead of having to do so repeatedly,
[01:00:40] when visiting individual websites. Privacy and consumer rights advocates, have been nervously waiting, for Newsom to sign the bill, which passed the California legislature, on September 11th. This is the first law, in the country, of its kind. The governor vetoed, a similar, but broader bill last year, which also applied, to mobile operating systems. Matt Schwartz, a policy analyst, at Consumer Reports, said, quote, these signals,
[01:01:09] are going to be available, to millions more people, and it's going to be much easier, for them to opt out, unquote. Until now, Schwartz said, individuals, who want to use, a universal opt-out, have had to download, third party browser extensions, or use a privacy, protective browser, you know, meaning Brave, DuckDuckGo, Tor, or Firefox, if you flip the switch on. Other bills signed by Newsom on Wednesday, also give Californians,
[01:01:38] important data privacy rights. One of them requires, social media companies, to make it easy, to cancel accounts, and mandates, that cancellation, lead to full deletion, of consumers data. A second bolsters, the state's data broker, registration law, by giving consumers, more information, about what personal data, data is collected, by data brokers, and who can obtain it. So I did some additional research, and found that this was measure,
[01:02:07] AB 566, relating to, opt-out preference signals. Unfortunately, it appears that we're not, going to be getting it, for another 14 months, since the new law, doesn't take effect, until January 1st, 2027. But at that time, all web browsers, will need to include, functionality for Californians, to send an opt-out, preference signal, to businesses, they visit online,
[01:02:36] through the browser. The law follows, the California Privacy Protection Agency, CCPPA, announcement, of a joint, investigative sweep, with privacy enforcers, in Colorado, and Connecticut, to investigate, potential non-compliance, with global privacy control, the GPC signal. So at least, we have some progress. Chromium browsers, will need to get, with the GPC plan, which just basically, means that Chromium,
[01:03:07] the Chromium core, is going to have to support it, as will Apple's Safari browser. And once we have GPC available, privacy enforcers, will then be able, to start investigating, who is and who is not, honoring, the clear preference setting, that will be sent, to all browsers. As we saw, do not track, you know, never got enforcement, you know, and just having a GPC signal, means nothing,
[01:03:37] if there's no penalty, for ignoring it. You know, and while we're at it, how about we also allow, our browsers, to send a cookie, acceptance preference signal, so that we can also, dispense with all of those, ridiculous, cookie permission pop-ups. That would be, a step forward for the, you know, the world's user interfaces. Anyway, it's, you know, it's progress. We have the technology, and then we have the legislation, to require its use,
[01:04:05] and that it actually be honored. So, you know, it takes years, but we're getting there. Last Tuesday, OpenAI posted a piece titled, Disrupting Malicious Uses of AI. This, this, their little blurb, pointed to a detailed, and lengthy, 37-page report, about their efforts, to block, many different abuses, of their technology.
[01:04:35] Among those cited, OpenAI, moved to disrupt, PR, PRC, you know, People's Republic of China, espionage operations. Their security team, banned, chat GPT accounts, used by Chinese, state-sponsored hackers, to write, spear phishing emails. The accounts were, allegedly used by groups, tracked by the, infosec industry, as UNK,
[01:05:04] drop pitch, and UTA 0388. The emails, targeted Taiwan's, semiconductor industry, US, academia, US think tanks, and organizations, representing Chinese minorities. OpenAI says, threat actors, primarily abuse its service, to improve phishing messages, rather than write malware, which is also, what the threat company, the threat intel company,
[01:05:33] intel 471, has observed. Okay, now, this is certainly a good thing, for them to do. We've noted, how phishing email, is no longer, obviously grammar impaired, making, you know, you know, basically removing, the first obvious sign, that you should hit delete, in your email, instead of bothering, to even read, the nonsense, that it's spewing. But I suppose, I'm not hugely impressed,
[01:06:02] because open AI, was likely being used, only because it was among, the lowest hanging, of the myriad, of available fruit. There are so many other sources, of the same, or similar, generative AI, assistance. I mean, the threat actors, could even spin up their own, as we know, that this feels like a battle, that will always be lost. You know,
[01:06:31] you know, just, it seems to me, that there's just no way, that AI, is not now going to, always be used, to improve the quality, of phishing mails, regardless of what barriers, any of the commercial providers, put up. There will always be, you know, alternatives, available. So, I guess I'm not, hugely impressed. It would be difficult,
[01:06:58] to find a better example, of the need, to continue supporting, long, past, its prime, website code, than is evidenced, by the fact that Microsoft, continues, believe it or not, to need, to offer the option, to reload, very old web pages, under, its creaky, old,
[01:07:28] IE mode. It's true. And I, in fact, this email went out, yesterday afternoon, and I, have already heard, from one of our listeners, who said, he just the other day, encountered an instance, where some government websites, would not run, under edge. And he had to, switch to IE mode, and then the page rendered. So, they're still out there. What's also true,
[01:07:58] unfortunately, is that IE's, old chakra, JavaScript interpreter, contains, known, exploitable flaws, that bad guys, want access to. We're talking about, this ancient history today, because it's apparently, less ancient, than we might hope. IE mode, is still being exploited, to the point that, Microsoft's, most recent iteration, of edge,
[01:08:27] has removed, all, of the easy, to click buttons, from the browser's UI. An unknown threat actor, has been tricking, Microsoft edge users, into enabling, internet explorer mode, in edge, to run their malicious code, in the user's browser, in order, to take over their machine. These mysterious attacks, have been conducted, since at least August, of this year, according to the,
[01:08:56] Microsoft edge security team. IE's legacy mode, or IE mode, is a, separate website, execution environment, within edge. It works by, reloading a web page, but running the, reloaded page, and its code, inside, the old, internet explorer engines. And as we know, Microsoft included, IE mode in edge, when it's, when it retired, its official, IE predecessor. And I guess we had, we had like,
[01:09:26] IE 11, I think was the last, version of IE, but, there were still some code, that was dependent upon it. So to access a site, under IE mode, previously, users, would have to press a button, or a menu option, to reload the page, from edge, into the old, IE execution environment. Microsoft has said, that it has received, credible reports, that hackers,
[01:09:55] were using clones, of legitimate websites, to instruct users, to reload the clone pages, in edge's IE mode. Oh God. Yep. Yep. And why would they do that Steve? Why? Well, when that happened, the malicious site, would execute, an exploit, chaining, an exploit chain, targeting IE mode, creaky old, chakra, javascript engine,
[01:10:25] that has bugs, that have never been patched, the exploit chain, contained a chakra, zero day, that allowed them, to run malicious code, and a second exploit, that allowed them, to elevate privileges, and take over, the entire user platform. Now, that's actually pretty ingenious, though. It is. I mean, if you think about it. if there's a way, these guys. They'll do it. So, in response, Microsoft did not assign, a CVE,
[01:10:54] nor release a patch. Instead, they overhauled, the entire, IE mode access. The edge security team, has completely removed, all the dedicated buttons, and menu items, that could once easily, refresh and relaunch, a website under IE mode. This includes, the dedicated toolbar button, the context menu option, and under the hamburger, main menu item. From this point on,
[01:11:24] anyone wishing, needing actually, to relaunch a website, in IE mode, will first, have to go into, the browser settings, and specifically, enable, the normally, disabled feature there. They'll then need, to relaunch the browser, you know, shut it down completely, relaunch their browser, and manually add, the URL, of a website, into an allow list, of sites, permitted,
[01:11:54] to be reloaded, in IE mode. So, I mean, they, you really have to need, it that way, but it does sound like, for those people, for example, who, who are using a government site, that is old and creaky, and only runs under IE mode, well, you can still do it. You just have, you know, you have to go in, and you turn it on, then you relaunch the browser, then you manually put, that government URL, into the allow list, and then,
[01:12:24] you'll be able to access it. So, it sure sounds as though, Microsoft is none too happy, that their old, internet explorer code, is still coming back, to bite them. So, they decided, that while they still, cannot safely, just kill it off, once and for all, at least they can make it, really much more difficult, to use, and thus, to abuse. So, that's good. Leo, break time, and then we're going to, look at, some news,
[01:12:53] that actually occurred, while I was putting, the show together, about, Salesforce customer, data leakage, and, we're going to get, to this horrifying, new Texas law, that takes effect, in 10 weeks, that Tim Cook, begged, not to have. Yeah, Apple's not thrilled, about what California, did either, although it's exactly, what you proposed, I think, in the past, which is that, the app store, ask people, when they're setting up, an account,
[01:13:24] are you 18, or over, are you over 18, and then if, or I guess, what they do is, they say, is this being set up, for somebody besides you, and what is the age, of this child, and then it's in the phone, and there's an API, that apps can query it, that seems like, such a sensible plan, it's what Meta wanted, Google even wanted it, OpenAI wanted, but Apple's kind of like, well, do we have to be responsible, for this well? Well, as we're going to see, in a few minutes, everybody's going to get it, as a result,
[01:13:52] of SB 2420. Yeah, oh, you're going to talk about, SB 2420, good, okay, good, yep, coming up, but first, a word from our sponsor, Vanta, what's your 2 a.m. security worry, what keeps you up at 2 a.m., is it, do I have the right controls, at place, or, is it, are my vendors secure, how about the really scary one, how do I get out, from under these old tools, and manual processes, well,
[01:14:21] well, enter Vanta, Vanta automates, manual work, so you can stop sweating, over spreadsheets, chasing audit evidence, and filling out, endless questionnaires, Vanta's trust management platform, continuously monitors, your systems, centralizes your data, and simplifies, your security, at scale, Vanta also fits, right into your workflows, using AI, to streamline, evidence collection, flag risks, and keep your program audit ready,
[01:14:51] all the time, isn't that nice, with Vanta, you get everything you need, to move faster, scale confidently, and get back to sleep, get started, at Vanta.com, slash, security now, that's V-A-N-T-A, dot com, slash, security now, thank you Vanta, for supporting the good work, Steve's doing here, at security now, and you support us, by going to, Vanta.com, slash, security now, okay Steve,
[01:15:22] excuse me, okay, here we go, wow, so, first of all, remember how I was saying, that we were almost certainly, going to soon be hearing news, of the leaks, of Salesforce customer data, just during the time, I was assembling today's show, the news broke, that the first tranche, of those nearly 1 billion,
[01:15:51] leaked Salesforce customer records, has been published, top of the list, was Qantas Airlines, and what do you know, the criminals were not dissuaded, by that permanent injunction, the Qantas CEO, managed to obtain, from Australia's Supreme Court, joining Qantas, in private database publication, we also have, Vietnam Airlines, Albertsons, The Gap, Fujifilm, and NG Resources,
[01:16:21] spelled E-N-G-I-E, Resources, and in the case, of Vietnam Airlines, who were mentioning, for the first time, the Scattered Lapsus, Hunters Group, leaked 7.3 million details, from Vietnam Airlines, customer loyalty program, which was data, taken from the company's, Salesforce account, so, the Salesforce said, nope, we're not paying you, your 3.5 million dollars,
[01:16:51] which, you know, doesn't really seem like that much, for 39, of their customers, all the data, of 39, of their customers, but, what are you going to do? Again, you know, I mean, they made a lot, big stink about it, everyone says, don't pay the bad guys, so, they're not going to, but, you know, their customers, customers, are paying the price. Wow. Okay, here we go. Last Wednesday, Apple's developer portal,
[01:17:21] posted their position, and response, to the Texas Senate Bill, SB, that's what, you know, Senate Bill stands for, SB, 2420, whose official title, is, relating to the regulation, of platforms, for the sale, and distribution, of software applications, for mobile devices. Okay, so, there's been a lot, of recent, child protective legislation, activity in Texas, recently,
[01:17:50] so things can get, a little bit confusing there. So, first, to clarify, this Senate Bill, 2420 legislation, which Apple is responding to, is not, the same bill, that recently, caused, Pornhub, to go dark, across Texas. Pornhub, suspended, its services, in Texas, because of a Texas law, that was passed, two years ago, back in 2023, that was House Bill,
[01:18:20] HB 1181. It was, that bill, was immediately challenged, in the courts, and it wound up surviving. That's the law, that requires websites, hosting a majority, of content, that's inappropriate, for minors, to proactively verify, the age of every single visitor, before they are allowed, to view the site's, contents, contents, lacking any accepted, privacy enforcing, means to do that, and given that we're now,
[01:18:50] seeing tens of thousands, of extremely personal, government ID scans, falling into criminal hands, during data breaches, which appears to be inevitable, Pornhub, probably correctly, determined, that the percentage, of people, who would be willing, to be fully, de-anonymized, during their visits, to their site, would not be appreciable, so just closing their doors, to Texans, was the right solution, for them. It's worth mentioning,
[01:19:19] that this Texas legislation, HB 1181, now having survived the courts, all the way up to, and including the Supreme Court, is likely to become a model, for other states legislation, which will therefore, not need to struggle, for adoption and enforcement, because Texas already did that, you know, verifying that the legislation, passed the court's scrutiny, so we might expect to see,
[01:19:48] many other states, driving adult content websites, out of their jurisdictions, simply by following, Texas's lead. Okay, but back to, Texas's newer legislation, which is Senate Bill, SB 2420. While its official title, is quote, relating to the regulation, of platforms, for the sale and distribution, of software applications, for mobile devices, it is commonly referred to as, the app store,
[01:20:18] Accountability Act. It regulates, how app stores, and software application developers, operating in Texas, must verify users' ages, and handle purchases, or downloads, by any minors, in the state. The legislation states, that the owners, and operators, of app stores, meaning, Apple and Google, right, must verify, must verify,
[01:20:46] a user's age, via a, commercially reasonable method, unquote, when an account is created. If a user is a minor, under 18, as defined in the bill, the legislation requires, that the minor's account, be tied to, you know, affiliated with, a parent's, or guardian's account. Additionally, additionally, each download, or purchase, by a minor,
[01:21:16] must first receive, explicit parental consent. And I'll, I'll expand on some of these points, in detail, from the language of the law. The store must also, clearly, and conspicuously, display, each app's age rating, and the content elements, that were used, to derive that rating. App stores, must limit, their data collection, and let me just, reinforce, this is going into effect, in 10 weeks. This is not, you know, 20,
[01:21:46] 29 or something. This is January 1st, 2026. This is happening. And I'll, I'll, I'll, I'll preempt something, I mentioned later. There's been no legislation, filed against this. Probably because people, after what happened, with HB 1181, no one's bothering. So, this is happening. App stores must limit, their data collection, to what is needed, for obtaining age verification, consent,
[01:22:16] and record keeping. And any violations, of any of these provisions, such as attempts, to obtain blanket consent, or making any misrepresentations, can be treated, as deceptive trade practices. Okay, so that's on the app store side. Software developers, have obligations, under this new legislation, as well. Developers, must assign, an age rating, to each of their apps, including any, in-app purchases.
[01:22:46] And those age assignments, must be consistent, with the age category, specified in the bill. Developers, must also substantiate, their age assignments, by providing the app content elements, which led to that rating. They must notify app stores, of any significant changes, to the app's terms, its privacy policy, changes in monetization, or features, or any change, in the app's resulting rating. Apps must use,
[01:23:16] the age and consent information, from the app store, to enforce age restrictions, to comply with the law, and enable any safety features. Apps must delete, any personal data, received, for age verification, once such verification, is completed. So that's, very good. That gives us, what we didn't see happening, with Discord, Zendesk deal. And any violations, such as, misrepresenting,
[01:23:45] the app's age rating, enforcing terms, against minors, without consent, wrongful disclosure, of personal data, and such, are actionable. However, there are some, liability protections. If the developer, follows, widely adopted, industry standards, in good faith, this new Texas law, states that they may be, exempt from liability. So, mistakes are understood. Okay, so until we had, this new Texas law,
[01:24:15] which was signed into law, by Texas Governor, Greg Abbott, and is scheduled, to take effect, on January 1st, 2026. So, in less than three months, App Store, and application age, and content ratings, were advisory only. App Stores, run by Apple and Google, were assigning age ratings, to apps, using self-regulatory frameworks, such as the IARC,
[01:24:43] the International Age Rating Coalition System. Developers answered questionnaires, about their apps, the stores would generate, an age rating, such as 12 plus, or teen, and display those indications. But all of those, were informational only. Nothing prevented, app acquisition, and download, by younger users. That, is the big thing,
[01:25:13] that SB 2420 changes. One of them, at least. Now, app developers, are legally required, to assign an age rating, using criteria, defined by this Texan law. App Stores, must display those ratings, and the specific content descriptors. And these ratings, now carry legal weight, and must be enforced, by App Store technology, to trigger,
[01:25:43] parental consent requirements, and enable, or disable, the app's download. And any developer, who misrates an app, or fails to update ratings, after material changes, can face liability, under deceptive trade practice law. Naturally, Apple, who sees privacy concerns, hiding around every corner, has not been happy, about any of this.
[01:26:13] And, Tim Cook is believed, to have called Greg Abbott, to argue against the provisions, of the legislation, asking Abbott, to either modify, or completely veto the bill. Those pleas, apparently fell on deaf ears. Apple's concerns, have been, that the new law, would require, sensitive, personally identifying, information, to be collected, from any Texan, who wants to download apps, even innocuous ones,
[01:26:42] such as weather apps, sports scores, et cetera. Yeah, because everything's, going to be designated, even if it's a weather app, I'm going to designate it, adults only, because I don't want to take, any chances, right? Right. Almost all apps, will be adults only. And, but get this Leo, even if it says, age two and above, still requires, got it, got it, anything, anything, anything, yes, anything, any, any app, downloaded by a minor,
[01:27:10] regardless of its rating, requires parental consent. I mean, parents are going to get fed up, having to say, yes, fine, you can download the port, the sports scores app. Anyway, Apple has warned of downstream data sharing, since SB 2420, requires app stores, to implicitly share, age and parental consent status, with developers. And, of course, the bottom line, is that Apple, really,
[01:27:40] really, really, really, doesn't want to do this, or get involved in any way, with any of this. However, that doesn't feel like, a practical long-term position, for Apple to be taking, given the legislation, which we're seeing. You mentioned California, that's, that, that's like, generous, compared to what, Texas is, is doing in 10 weeks. Everything we see everywhere,
[01:28:10] evidences a growing awareness, of age-related, internet content control. Okay, so I started out, noting, that last Wednesday, Apple's developer portal, posted their position, and response, to these new Texas requirements. Apple's posting, was titled, New Requirements, for Apps Available in Texas. And Apple writes, Beginning January 1st, 2026,
[01:28:39] a new state law in Texas, SB 2420, introduces age assurance requirements, for app marketplaces, and developers. While we share the goal, of strengthening, of strengthening, kids online safety, we're concerned, that SB 2420, impacts the privacy, of users, by requiring, the collection, of sensitive, personally identifiable, information, to download, any app, even if a user,
[01:29:08] simply wants, to check the weather, or sports scores. Apple will continue, to provide parents, and developers, with industry leading tools, that help enhance, child safety, while safeguarding privacy, within the constraints, of the law. Once this law, goes into effect, users located in Texas, who create, a new Apple account, and I'll come back to this, but this is interesting, Leo, create a new Apple account. There is no language,
[01:29:38] that is retroactive, in this legislation, which is really interesting. Apple said, will be required, to confirm, whether they are, 18 years or older. Again, required to confirm, whether they're, 18 years or older. That means everybody, I mean all adults. All new Apple accounts, for users, under the age of 18, will be required, to join,
[01:30:07] a family sharing group, and parents, or guardians, will need, to provide consent, for all, app store downloads, app purchases, and transactions, using Apple's, in-app purchase system, by the miner. This will also, impact developers, who will need, to adopt new capabilities, and modify behavior, within their apps, to meet their obligations, under the law, in 10 weeks. Similar requirements,
[01:30:36] will come into effect, later, next year, in Utah, and Louisiana. So, Texas alone, for now, here comes Utah, and Louisiana. So, and just wait, till Mississippi, gets wind of this, and figures out, that they can do, the same thing. Apple continued, today, we're sharing details, about updates, we're making, and the tools, we'll provide, to help developers, meet these new requirements,
[01:31:04] to assist developers, in meeting their obligations, in a privacy preserving way, we'll introduce capabilities, to help them obtain, users age categories, and manage significant changes, as required, by Texas state law. The declared age range, API, is available, to implement now, and will be updated, in the coming months, I hope it's in weeks, to provide,
[01:31:33] the required age categories, for new account users, in Texas, and new APIs, launching later this year, meaning, in time, this year, will enable developers, when they determine, a significant change, is made to their app, to invoke, a system experience, to allow the user, to request, that parental consent, be re-obtained, additionally, parents will be able, to revoke consent,
[01:32:02] for a minor, continuing to use an app, more details, including additional, technical documentation, will be released, later this fall, in other words, Apple is scrambling, in order to provide, the API, which, the APIs, that developers, will need, in order to be, compliant, with this Texas law, they said, we know, protecting kids, from online threats, requires constant vigilance, and effort, that's why, we will continue, to create,
[01:32:32] industry leading features, to help developers, provide age appropriate, experiences, and safeguard privacy, for their apps, and games, and empower parents, with a comprehensive, set of tools, to help keep, their kids safe online, online, okay, so I, I went over, to check out, Apple's, declared, age range, API, the page is titled, declared, age range, create, age appropriate, experiences, in your app,
[01:33:01] by asking people, to share, their age range, okay, I was struck, by the language, by asking people, to share, and by the name, of the entire API, the API, which is after all, the declared, age range, API, what follows then, is the overview, of the API, on the page, and it just says, you know, so here's the overview, of the declared, age range, API,
[01:33:31] says, use the declared, age range, API, to request people, to share their age range, with your app, for children, in a family sharing group, a parent, or guardian, or the family organizer, can decide, whether to always share, a child's age information, with your app, ask the child, every time, or never share, their age information, along with an age range, the system returns,
[01:33:59] an age range service, dot age range, declaration object, for the age range, a person provides, this is Apple, compliance, with the California law, because it doesn't work, with the Texas law, right, right, right, so the California law, does exactly that, it says, a maker of an app store, or operating system, by the way, the California law, would apply to Linux, has to, ask for an age, of the user, and then have an API,
[01:34:29] that returns that age range, and it's like, zero to, zero to five, five, it's like four, five to ten, ten to thirteen, thirteen to sixteen, sixteen to eighteen, or at eighteen, or over, but that satisfies California, you're about, I mean, there's no way, this satisfies, what Texas is asking for, no, no, just wait, till we get to the specifics, yeah, so, but even on Apple's page, in a vividly highlighted call out box, labeled important,
[01:34:59] the page states, data from the declared age range API, is based on information, declared by an end user, right, or their parent, or guardian, you are solely responsible, for ensuring compliance, with associated laws, or regulations, that may apply to your app, so, you know, Apple is saying, we're not, we're not responsible, for verifying,
[01:35:28] what this, what is declared, as the user's age, so, exactly to your point, Leo, none of this, is useful, for Texas, right, and so, you know, this is Apple saying, that all they're doing, is here, is functioning as a middleman, to pass along, whatever age declaration, the user might assert, and that the app's developer, in this instance, remains responsible, for ensuring compliance,
[01:35:57] with associated laws, or regulation, so, this of course, begs the question, what does the forthcoming, Texas SB 2420 law, require, in that regard, we know, that in other jurisdictions, and contexts, self-declaration, of age, is specifically regarded, as insufficient, so what about Texas, because kids are going to lie, they're going to say, I'm 18, of course, of course, I'm 18, honest, yeah, yeah, the bill does not mandate,
[01:36:28] a single specific age, verification method, such as uploading an ID, but it does require, app stores, to use a quote, commercially reasonable method, to verify, a user's age, not just accept, whatever age, the user may self-declare, so as a clarifying, example, the legislation states, that app stores, may not rely, on a birth date, entered into a form,
[01:36:56] or any other method, that is quote, reasonably likely, to be circumvented, by a minor, so I've been studying, this carefully, in an attempt to understand, how and whether, Apple's declared range API, is in any way, sufficiently responsive, to what Texas requires, you know, clearly it's not, the only way I can see, that it could be applicable, would be, if Apple starts out, with declared age,
[01:37:25] then later replaces, the declaration part, with a full, some sort of full, responsibility taking, verifiable, age determination mechanism, because that's what Texas requires, and in that way, the same API, could be used, and just the source, of the age determination, information would change, and Apple has said, that there, they will have other new APIs,
[01:37:56] you know, later this year, there's not much, of this year left, so, I'm sure, they're working on it, so for example, what could be done, state by state, or political jurisdiction, by jurisdiction, would allow, self-declaration, to continue, to be sufficient, within regions, that have not yet, clamped down, on their citizens, and only using, and requiring, verifiable age, verification,
[01:38:26] where the governing laws, require, that it be used, so what Apple has today, with their family sharing, is that, Apple asks, for a date of birth, during account creation, for accounts under 13, Apple requires, an adult parent, or guardian, to be a member, of the family group, and for ages, 13 through 17, a teen can create, their own Apple ID, without parental verification, with Apple trusting,
[01:38:55] the date entered, which seems screwy to me, if you were 12, why not, that, what prevents you, from just declaring, that you're 13, again, Apple historically, has done what they can, not to get involved, in all this, all of this changes, in 10 weeks, it all dies, in Texas, on New Year's Day, what's required, by Texas SB 2420,
[01:39:24] is an affirmatively, commercially reasonable, method of age verification, for every, account, created, self-declaration, never, is sufficient, in Texas, this implies, that for Texas users, Apple will need, Apple, will need to implement, some new form, of age verification, ID checks, credit card based validation, or some other form, of verifiable,
[01:39:53] age assurance technology, and Apple has fewer, as I've mentioned, than three months, to bring this online, while Apple, currently only requires, and enforces, parental linking, for account owners, younger than 13, SB 2420, specifically applies, to all minors, under 18, under Apple's, current family sharing plan, the so-called, it's asked to buy option,
[01:40:22] is available to parents, who may choose to enable it, for their kids, but it can be disabled, and parents can also choose, to grant blanket permissions, under SB 2420, blanket, or any form, of pre-authorized permission, is expressly forbidden, in the law, it states it, under SB 2420, Perel consent, is legally required, for every,
[01:40:52] app download, and in-app, purchased by any minor, imagine, being a 17-year-old, high school senior, in Texas, and needing to obtain, your mother's permission, to add an app, any app, regardless of its age rating, to your iPhone, I mean, Leo, think of, I mean, think of all the apps, we've downloaded, just because it was easy, it was, you know,
[01:41:22] just to see what they were, now, well, anything that, if accesses the internet, like a browser, would probably have to be, marked adult, only, right, good point, kids, kids are not going to have, much access to anything, except kiddie stuff, right, explicitly for kids, it's a mess, the language of the law, quote, from the, from the, the,
[01:41:51] the, from the text, of the, legislation, it says, an operator, of a digital distribution, platform, app store, shall obtain, verifiable parental consent, before allowing, a minor to download, or purchase, any software application, through the platform, unquote, and also, quote, parental consent, must be obtained,
[01:42:22] on a per transaction basis, and may not be granted, as a blanket authorization, unquote, so anyway, it's not difficult to see, why Tim Cook, would have given, Greg Abbott a call, to plead with him, to amend, or to veto this, veto this legislation, one interesting aspect, of the legislation, is that nothing in it, appears to apply, retroactively, as I noted, the age verifications, are only performed,
[01:42:51] upon new account creation, however, existing adult accounts, might need to have, their adult status, reasserted, you know, verified, if a minor's account, were to be linked, to it as a parent, or guardian, so, wow, whatever the case, this new Texas SB 2420, legislation, is going to create a mess, and it's only about, 10 weeks away,
[01:43:21] from coming into effect, so far, the law has not been, challenged in court, as I mentioned, and I assume, that's because, Texas's earlier, HB 1181 legislation, survived, both the Fifth Circuit, Court of Appeals, and then the U.S. Supreme, Court's analysis, so under the current, U.S. legal climate, it might be viewed, as a fait accompli, that's not even worth fighting, which leaves us, with a question, how is Apple,
[01:43:49] going to verifiably, determine, the ages, of any new, account holders, in Texas, one thought, occurred to me, which is, perhaps an age verification, performed, at the purchase time, of a new iPhone, you know, you're buying it, with a credit card, presumably, or mom and dad, are buying it, for their kids, so, perhaps, you tie, age verification, to purchase, but you know,
[01:44:19] but then you have the problem, going forward, of, of new accounts, being created, any new account, created, will need to have, its age determined, and it does seem like, a huge loophole, in, in SB 2420, that there doesn't appear, to be any retroactive, action here, so, I don't understand that, Leo, but boy, you know, and, if Apple has to do this, in Texas,
[01:44:48] and if it's coming, in Utah, and Louisiana, and Lord knows, Yeah. Yeah. Because, as you've pointed out, geo IP location. Yeah. Yeah, geo locate, I mean, IPs were not designed, to be, you know, about states, of the US, and, and they're not, very much so. Okay, break time, and then, we're going to look at, the interesting, site makeover, that the Breach Forums,
[01:45:20] Scattered Spider Lapsus Hunters, site, recently got. Okay. But, our show today, brought to you by, the Thinkst Canary, let's talk about, how you defend yourself, against Scattered Spider Lapsus, and all the other, little critters, floating around the internet. And, the real issue, of course, is how do you know, if they've penetrated, your defenses? You're going to have, defenses money can buy. But, what if they get in? The problem is, most companies,
[01:45:50] don't know for 91 days, on average, that they've been breached. That's three months, that the bad guys, can do what they did to Salesforce, which is wander around inside, exfiltrate everything, what was it, terabytes? How many terabytes of data? 1.6. Nobody was, like, they didn't know. They weren't paying attention. Wouldn't it be nice, if you knew? That's why you need, our sponsor, and their wonderful, Thinkst Canary.
[01:46:19] You've heard me talk about it before. It's a honeypot. It's a honeypot that is secure, is super easy to use, you can deploy it in minutes, and it tells you, if somebody's entered your network. Here's my, my Thinkst Canary, interface here. You see, I have one Thinkst Canary, the one in the attic. Oh, wait a minute, I have an alert. Let's see what it is. It says, oh, the device was reconnected. Yes, I moved it over to my desk, so I disconnected it.
[01:46:49] That's how, I know it's still alive, because I get that little notification. You can even, if you want, you can, you can look at all of the, you can get the audit trail and see all of the notifications you've received, whether there were incidents, when they were notified. So, I don't know what seasonal effects are, but I've, I've disabled, enabled them, disabled them, and re-enabled them. I can't remember what I did, but that's the point. You've got an audit trail. You've, you've got a device
[01:47:17] that can be anything. As I said, it is, it is a honeypot, which means it's posing. It's not really, in my case, a 2019 Windows Server Office file share. It's just posing as that. But when I say pose, I mean, it's really posing. It's got a Microsoft Mac address. It, in every respect, looks exactly like it was pretending to be. But it's not limited to Windows servers. It can be almost anything.
[01:47:45] An active directory domain controller, SharePoint. It can be a Linux box. It could be an Oracle Enterprise server. It could be Mac OS X file share. A Cisco router. A Dell switch. A FortiGate. A Palo Alto firewall. I can go on and on and on. It can even be a SCADA device. It could, it could be a Synology. You could, so the point is, make it something you think a bad guy will find valuable. Or maybe vulnerable. Like,
[01:48:14] what if I decided to make it a, I don't know, Windows XP desktop. File share. Yeah, baby. That sounds good, doesn't it? You can turn on, you can make it a Christmas tree, turn on all the services, or just a few select, let's turn on an SSH server. Yeah, that's good. And I want to leave it on port 22. No, wait a minute. I'm not. Because I'm going to be clever, and the bad guy's going to look at me and say, oh,
[01:48:44] he's trying to hide it on port 22346. Ha! Not going to fool me, says the bad guy. I'll discard the changes for now, just so I can show you some other features. These are the Canary tokens. These are files that, when accessed, will let you know. And you can put these anywhere. I've got them scattered all around. They can be everything. An AWS API key, a Microsoft Word or Excel document, a WireGuard VPN client config.
[01:49:14] Oh, that would probably have the private address, wouldn't it? That sounds like a good thing to stick around. Put it on your, put it on your Google Drive, or your OneDrive. Put it, put it on your hard drives. Put them everywhere. When these Canary tokens are hit, or somebody brute forces that fake internal SSH server I just set out, your Thinks Canary will immediately tell you, hey, you've got a problem. No false alerts, just the alerts that matter. And in any way you want, SMS, email,
[01:49:44] it supports syslog, it supports web hooks. There's even an API if you want to write your own interface. So it's very simple. You just choose a profile for your Thinks Canary device. You register it with a hosted console for monitoring and notifications. And then you sit back and wait. Attackers who have breached your network, malicious insiders, and other adversaries, they can't help it. They see that Windows XP file share sitting there. And they say, I gotta go after that.
[01:50:13] They make themselves known just by accessing your Thinks Canary. It's the best honeypot ever. And it's absolutely secure. The folks at Thinks have many years teaching enterprise and governments how to break into systems. So they know all the ways of the wily hacker. They've been themselves. And so they've made sure that this is a bulletproof solution. Absolutely secure solution.
[01:50:43] It does one thing. Let's you know when a bad guy has entered your network and is attacking your Thinks Canary. Visit canary.tools.twit. If you're a big bank, you might have hundreds of them. Every segment should have at least one, right? A little business like ours might just have a handful. Let's say you need five. $7,500 a year. You get five Thinks Canaries. You get your own hosted console. You get upgrades. You get support. You get maintenance.
[01:51:11] By the way, if you use the code TWIT in the How Did You Hear About Us box, you're going to get 10% off that price for life. And the other thing that's good to know, you can always return your Thinks Canaries with their two-month money-back guarantee for a full refund. However, during all the years we have partnered with Thinks Canary, their refund guarantee has never been claimed. Visit canary.tools.twit. Visit canary.tools.twit. Enter the code TWIT in the How Did You Hear About Us box.
[01:51:40] You're going to get that 10% off, not just for the first year, but for as long as you have your Thinks Canaries. canary.tools.twit and the offer code TWIT. Yeah, that's a good one. Flow Connect says, I'm going to be a solid state drive that says adult videos on it. That'll get them. You get to do whatever you want. I'm not going to tell you what to do. It's actually fun to play with a configurator. Canary.tools.twit. Use the offer code TWIT.
[01:52:08] These are honeypots that are easy to set up, easy to maintain, and they do the job. And that's the most important. Now, back to Mr. Steve Kipps. So this was a little bit tongue-in' cheek. I described what happened to Scattered Spider Lapses Hunter's ransom forum as a makeover because breachforums.hn is no longer showing
[01:52:38] the extortion notice that we had in the show notes last week. Ah, ah. And then we have the Department of Justice seal. The FBI's investigation looks like, what is that? Spain? The Brigade de Lutte contre le Cibercriminal. Yeah, and then certainly France.
[01:53:08] France. Yeah, yeah. So Parquet de Paris. Breachforums.hn. HN is the top-level domain for the Central American country of Honduras. So the FBI has taken over that domain's DNS, pointed it to one of their servers. So for anyone who goes over to breachforums.hn, whoopsie, they're not home anymore. I like the email address on the new page, breachforums
[01:53:38] at fbi.gov. Yeah, just give them a ring. Wow. Wow. Yeah. So Grey Noise has detected and reported a widespread botnet-driven attack, which began last Wednesday, so six days ago on the 8th of October. That attack is being sourced by more than 100,000 individual bots
[01:54:07] scattered across the globe, all aimed at U.S.-based exposed RDP endpoints. Now, as we know all too well, RDP is Microsoft's very poorly authenticated remote desktop protocol, which keeps being used because it works so well and it's built in. It's so easy. It's so handy. Yes.
[01:54:37] Unfortunately, it has also been an unending source of remote network intrusions through the years as bugs and other various failings have continued to be found in its code. Now, just to be clear, I love RDP. It works incredibly well and I use the crap out of it. But nowhere among any of GRC's internet-facing IPs and ports will anyone
[01:55:06] ever find any exposed RDP service because for me or anyone to publicly expose any instance of RDP to the internet would be just begging for an intrusion. Yes. So, I have three words. Don't do it. I thought you were going to say VPN, but okay. Don't do it. Don't do it. Don't expose it. those are a good three also because you need to have some way to not do it.
[01:55:36] But one way or another, arrange to don't do it. Don't do it. Okay. Okay. Now, unfortunately, my repeated admonishment flies in the face of convenience, right? As we all know, convenience often trumps security. You know, it's like, why would the great and powerful Microsoft allow us to turn it on if it wasn't secure? And my God, it's so handy. Right.
[01:56:05] A Shodan search for remote desktop protocol returns on the order of 2.4 million results. Some sources have claimed that Shodan has indexed more than 3.5 million exposed RDP ports, and some non-Shodan research has shown 4,493,357
[01:56:36] exposed RDP services when scanning for RDP running on a default port of 3389. All of this, all of this RDP nonsense is very nicely covered by one of the most important lessons all of us who've been participating together in this podcast for the past 20 years have learned. Authentication is generally broken and should never be trusted. The only
[01:57:06] internet servers that should ever be placed onto the internet are those that do not use any authentication. Authentication that's never used can never be broken because there isn't any. So things like web servers and DNS servers and email servers which are designed and intended to be accessible by anyone anywhere whose entire purpose is that they are for use by anyone
[01:57:35] anywhere they're safe to deploy but anything that requires any form of authentication is inherently risky. The only exception to this and I even hesitate but I got to be a little reasonable. The only exception is that I would be inclined to trust well-tested and carefully vetted connections to SSH servers
[01:58:05] running on a non-standard port if those connections are authenticated with cryptographically secure certificate credentials. But even there wherever possible filter all incoming connections by region. If you never roam outside of your own country why would you ever entertain connections from China Russia
[01:58:34] or Iran? You know none of those people are friends of the West. Don't even consider accepting their traffic to your non-public servers. use some geofencing to drop any traffic coming into authenticated endpoints if its IP is foreign. Why not? Gray Noise wrote since October 8th, 2025, Gray Noise has tracked a
[01:59:03] coordinated botnet operation involving over 100,000 unique IP addresses from more than 100 countries targeting remote desktop protocol services in the United States. The campaign employs two specific attack vectors, RD web access timing attacks and RDP web client login enumeration. Again, you can never
[01:59:33] trust authentication. Don't. with most participating IPs sharing one similar TCP fingerprint indicating centralized control. Source countries include Brazil, Argentina, Iran, China, Mexico, Russia, South Africa, Ecuador, and more than 92 others. So I would only ask that everyone
[02:00:02] consider filtering and dropping any traffic coming into any non-public authenticating services. You know you don't need or want that traffic. You should never assume that your authentication will hold. All of our experience says it probably won't. Blocking and dropping traffic that you know you don't want is what firewalls are for.
[02:00:32] But firewalls won't help if they're not used. So again, you'll never find RDP at GRC even though I use it like crazy. A listener of ours, Dan Linder, wrote, this well-respected UI slash UX organization agrees the new iOS 26 interface is a
[02:01:02] mess. They clearly describe a lot of our feelings well. I hope Apple listens. And he provided a link to the nngroup.com slash articles slash liquid hyphen glass. And of course, Dan is posting this at least impartial response to last week's UI rant where I detailed my feelings about the unproductive nonsense that Apple had added to their user
[02:01:31] interface. Forgetting the number one rule of UI design, which is that the interface should never call attention to itself for its own sake and should do everything it can to disappear and to facilitate the user's use of whatever it is it's interfacing. So, the brief TLDR summary at the top of the wonderful takedown piece reads, quote,
[02:02:00] iOS 26's visual language obscures content instead of letting it take the spotlight. New, but not always better, design patterns replace established conventions. I just want to share a bit of the piece, which begins, with iOS 26, Apple seems to be leaning harder into visual design and decorative UI effects, but at what cost to
[02:02:29] usability? At first glance, the system looks fluid and modern, but try to use it, and soon those shimmering surfaces and animated controls start to get in the way. Let's strip back the frost and look at how these changes affect the real use. iOS 26 introduces Apple's new glassmorphic visual language into its phones. Apple describes liquid
[02:02:59] glass as a translucent material that reflects and refracts its surroundings while dynamically transforming to help bring greater focus to content, delivering a new level of vitality across controls, navigation, app icons, widgets, and more. Translated, they write, the interface now ripples and shimmers as if your phone were
[02:03:29] encased in jello. At first glance, it does look cool, but problems arise as soon as you start actually using your phone. Transparency equals hard to see. Liquid glass makes UI elements translucent and bubbly. The result is light, airy, and often invisible. One of the oldest findings in usability is that anything placed on top of something else becomes harder to see.
[02:04:00] Yet here we are in 2025 with Apple proudly obscuring text, icons, and controls by making them transparent and placing them on top of busy backgrounds. Text on top of images is a bad idea because the contrast between the text and the background is often too low. So why does Apple now encourage users to set photos as backgrounds for translucent
[02:04:29] text messages? The result is that your friends' words are camouflage against their beach vacation photo, or worse, their pet's fur. content may technically be in focus, but you can't read or see it. And then comes Apple's boldest or dumbest experiment, text on top of text. Apparently designers decided users have eagle vision and infinite patience
[02:04:59] because deciphering one line of text written across another is now fair game. Reading an email subject line now requires Dan Brown level cryptographic decoder skills. Not only is it illegible, it's also ugly. Okay, and while this goes on and there's much, much more, I'll just finish by sharing this piece verbatim because if you recall my rant last week, you'd be inclined to
[02:05:29] wonder whether I had written this one too. The section heading is animated buttons motion without meaning and it reads animations can be delightful the first time. When used intentionally, they can also be satisfying, creating the feeling when someone just clicks or snaps into place. Our eyes are finely tuned to detect motion, which is why animated
[02:05:59] buttons grab attention instantly, but delight turns to distraction on the 10th, 12th, or 100th time. In iOS 26, controls insist on animating themselves, whether or not the user benefits. Carousel dots quietly morph into the word search after a few seconds. Camera buttons jerk slightly when tapped.
[02:06:28] Tab bars bubble and wiggle when switching views, and buttons briefly pulsate before being replaced with something else entirely. It's like the interface is shouting, look at me, when it should quietly step aside and let the real star, the content, take the spotlight. So anyway, I thank Dan for sharing another view
[02:06:57] posted last Friday by a group that specializes in UI design. Dan says, I hope Apple is listening. I'm glad it's possible to turn those superfluous wiggles, jiggles, zips, and zings way down to a tolerable level. Yeah, in accessibility you can turn it almost off entirely. But just as a footnote, who is NNG? It's the Nielsen Norman group. And I've interviewed Jacob Nielsen and Don Norman both.
[02:07:27] They are the king. Legendary. They're the legends. In fact, Don Norman's incredible book, the usage of everyday things is one of the best things ever written about usability. Bible on UI. Yeah. So this is not just any company. This is the UI company. And you know what? I've been putting up with liquid glass, trying to get used to it. And now that I read this article, I'm really not going to get used to it.
[02:07:58] I guess you can kind of turn it down. But what was Apple thinking? I really have to wonder. I just think maybe something's in the water or they're just so self-obsessed. It's truly awful. It's really bad. It's truly awful. Yeah. Yeah. I mean, it really, I mean, it does, it really, I mean, it's like a game. I don't, I don't, I, you know, there are games you can play on your phone, but you don't want your phone to be
[02:08:27] the game. It's terrible. If you shake it hard enough, does it come out the end? I wish it would like toothpaste. Gosh. Okay. Last break. Then we're going to look at what happened with the Redis server. Oh, all right. Yes, Steve, what happened? We're going to talk about that in just a moment. But first, a word from our sponsor, this episode of Security Now, brought
[02:08:57] to you by Big ID, the next generation AI-powered data security and compliance solution. Big ID is the first and only leading data security and compliance solution to uncover dark data through AI classification to identify and manage risk, remediate the way you want and to map and monitor access controls plus scale your data security strategy along with unmatched coverage for cloud and on-prem
[02:09:27] data sources. Big ID also seamlessly integrates with your existing tech stack and allows you to coordinate security and remediation workflows. You can take action on data risks to protect against breaches. You can annotate, delete, quarantine, more based on the data, all while maintaining an audit trail. It's great for compliance and it works with everything used. Partners include ServiceNow and Palo Alto Networks, Microsoft, Google, AWS, and on and on. With Big ID's advanced AI
[02:09:56] models, you can reduce risk and accelerate time to insight, plus gain visibility and control over all your data. Intuit named it the number one platform for data classification and accuracy, speed, and scalability. But I've got an even better testimonial because Big ID equipped probably the one organization with the most dark data in the world, the United States Army, to illuminate dark data. I mean, they have hundreds of years of dark data, right?
[02:10:26] To accelerate cloud migration, to minimize redundancy, and to automate data retention. All of these were very high priorities for the Army. U.S. Army Training and Doctrine Command gave us this great quote, quote, the first wow moment with Big ID came with being able to have that single interface that inventories a variety of data holdings, including structured and unstructured data across emails, zip files, SharePoint, databases, and more.
[02:10:56] To see that mass and be able to correlate across those is completely novel. I've never seen a capability that bring this together like Big ID does, end quote. CNBC recognized Big ID as one of the top 25 startups for the enterprise. They were named to the Inc. 5000 and the Deloitte 500, four years running. The publisher of Cyber Defense Magazine says, quote, Big ID embodies three major features we judges look for to become winners.
[02:11:26] Understanding tomorrow's threats today, providing a cost-effective solution, and innovating in unexpected ways that can help mitigate cyber risk and get ahead of the next breach. Start protecting your sensitive data wherever your data lives at bigid.com slash security now. Get a free demo to see how Big ID can help your organization reduce data risk and accelerate the adoption of generative AI. Again, that's
[02:11:56] bigid.com slash security now. Also, there's a free white paper that provides valuable insights for a new framework. It's AI trust, risk, and security management to help you harness the full potential of AI responsibly. You'll find that at bigid.com slash security now. Thank you, Big ID, for supporting Steve's work here. You support us too by going to this address, bigid.com
[02:12:25] slash security now. And now back to the show. Oh, boy. So, a trio of researchers at WIZ, that's W-I-Z as in wizard, research, they worked through Trend Micro's Zero Day initiative to disclose the significant problem they uncovered in Redis servers, which are
[02:12:55] exposed over the public internet. Why? It's hard to understand. We already know from today's episode, that this vulnerability has received the difficult to obtain CVSS score of 10.0. You know, 9.8 is normally the limit. You can't, it's difficult to get beyond 9.8, and 9.8 are really bad zero days. This is a 10.0. The reason this has come to the attention of the internet
[02:13:25] community is that there are, get this, nearly 330,000, a third of a million, 330,000 publicly exposed Redis or Redis servers on the internet, with around 60,000 of those, which require no authentication. They're wide open, ripe for exploitation. now, Redis,
[02:13:55] R-E-D-I-S, stands for Remote Dictionary Server. It was created back in 2009 by Salvatore Sanfilippo, who built it to solve his own problem, performance issues with his startup company. He initially created it to improve the performance of a real-time web analytics system. But the speed of an in-memory network accessible
[02:14:24] dictionary ended up being so useful that it evolved into a standalone open-source project of its own. Since then, it's evolved beyond a simple key value cache into a full in-memory data structure server. Unfortunately, that means there's a lot of data stored out on the internet in all these servers, and they're on networks, and unfortunately, they're penetrable.
[02:14:54] Now, I run a Redis server for Windows to improve the performance of the PHP-based web forums. I've got my Redis server bound to the local host IP 127-001 and listening on its default port of 6379. So, a number of the PHP-based services on that server take advantage of Redis to improve their performance.
[02:15:25] What I'm doing differently, and Leo, what I'm sure you're doing differently from 330 other instances is that the last thing I would ever think of doing would be binding the Redis service to any network interface that's connected to the public internet. I use RDP for that. Is that okay? No, of course not. Historically, you know,
[02:15:55] there have been thousands of botnet infections and data leaks due to open Redis ports. I mean, it has been a magnet for exploitation. So, on the one hand, nothing horrible involving Redis would be the first time, but what's been found is still new and maybe worse than anything. The guys at Wiz Research titled their report, Redis Shell, Critical
[02:16:24] Remote Code Execution Vulnerability, CVE 2025, 49, 844. In Redis, 10 CVSS Score. And their tease was, Wiz Research discovers vulnerability stemming from 13 year old bug present in all Redis versions used in 75% of cloud environments.
[02:16:54] So, they wrote, Wiz Research has uncovered a critical remote code execution vulnerability, CVE, which we've dubbed Redis Shell, in the widely used Redis in-memory data structure store. The vulnerability has been assigned a CVSS score of 10.0, the highest possible severity. The vulnerability exploits a use-after-free memory corruption bug,
[02:17:23] there's use-after-free again, that has existed for approximately 13 years in the Redis source code. This flaw allows a post-auth attacker to send a specially crafted malicious Lua script, a feature supported by default in Redis, to escape from the Lua sandbox and achieve arbitrary native code execution on the Redis host. This grants
[02:17:53] an attacker full access to the host system, enabling them to exfiltrate, wipe, or encrypt sensitive data, hijack resources, and facilitate lateral movement within cloud environments. Given that Redis is used in an estimated 75% of all cloud environments, the potential impact is extensive. Organizations are strongly urged to patch instances
[02:18:22] immediately by prioritizing those that are exposed to the internet. And again, why any R? I have no idea, but almost a third of a million are, and 60,000 of them require no authentication at all, so being post-off means post nothing. On October 3rd, they wrote, Redis released a security advisory along with a patched version of Redis. We extend our gratitude to the entire Redis team for
[02:18:52] their collaboration throughout the disclosure process. We greatly appreciate their transparency, responsiveness, and partnership during this engagement. In this post, we will provide a high-level overview of our discovery and its implications. Given the prevalence and sensitivity, they didn't say severity, but I would, of this vulnerability, we will defer some of the technical details to a future installment,
[02:19:22] omitting exploit information for now to allow impacted organizations sufficient time to address the vulnerability. Organizations utilizing Redis are strongly encouraged to update their Redis instances to the latest version immediately. And I'll just note also, exposure to the internet is bad, but when bad guys get into a network through any means,
[02:19:51] they look around for some means of obtaining a foothold, some other server which they can access which is vulnerable from the inside. So even Redis sitting inside a network containing a remote full remote code execution, native code execution on the host would be a juicy target for somebody to jump onto once they got inside
[02:20:21] and were sitting on a machine they couldn't do anything with, they'll start looking around for one they can. So there are plenty of public targets, that's going to be a problem, but all Redis everywhere should be updated. They wrote, the newly discovered Redis shell vulnerability in Redis has been assigned a CVSS of 10, 300 vulnerabilities receiving
[02:20:51] it in the past year. So yes, rarefied as we've said. It's also the first Redis vulnerability to be rated as critical. The score reflects not just the technical severity of remote code execution, but also how Redis is commonly used and deployed. Redis is widely used in cloud environments for caching, session management, and sub pub sub messaging. While Redis
[02:21:20] has had a strong security history, the combination of this flaw and common deployment practices significantly increases its potential impact. The vulnerability is a use-after free memory corruption that allows an attacker to send a malicious Lua script that leads to arbitrary code execution outside Redis' Lua interpreter sandbox, gaining access to the host. The urgency with which you should address this
[02:21:50] vulnerability depends upon how Redis was installed and its exposure level. Our analysis across cloud environments revealed the extensive scope of this vulnerability. Approximately 330 Redis instances are exposed to the internet at the time of this blog post. about 60,000 instances have no authentication configured. 57%
[02:22:19] of cloud environments install Redis as container images, many without proper security hardening. The official Redis container by default does not require authentication. Our analysis shows that 57% of cloud environments install Redis as an image. If not installed carefully, these instances may lack authentication entirely. The combination
[02:22:49] of no authentication and exposure to the internet is highly dangerous, allowing anyone to query the Redis instance and specifically send LUIS scripts which are enabled by default. This enables attackers to exploit the vulnerability and achieve remote code execution within the environment. Redis instances are also frequently exposed to internal networks where authentication may not be prioritized, allowing any
[02:23:18] host in the local network to connect to the database server. An attacker with a foothold in the cloud environment could gain access to sensitive data and exploit the vulnerability to run arbitrary code for lateral movement into sensitive networks. So they conclude their report, as they promised, without disclosing any of the critical details behind their discovery because Redis has been updated to cure this 13-year-old
[02:23:47] vulnerability and because they most want the world to update. Sadly, we pretty much know how that's going to go. And given that Redis is a widely used open source project, it will not be difficult for the bad guys, now knowing that there is a huge vulnerability in all of the past 13 years of open source Redis to determine what has been broken for the past 13 years and
[02:24:17] start scouring the internet for networks to attack and infiltrate. Also, since Redis is almost ubiquitously available on internal networks, even when instances are not publicly exposed, attackers will be able to scan the internal network for anything answering on port 6379 to see whether they found a long-ignored instance of Redis, which no one ever bothered to update, which would allow them, as I mentioned before,
[02:24:47] to pivot their attack into that machine to obtain a deeper foothold inside the network. The Wiz guys, which first demonstrated this during the Berlin Pwned Own competition, by the way, concluded their write-up, writing, Redis shell represents a critical security vulnerability that affects all Redis versions due to its root cause in the underlying Lua interpreter. With hundreds of thousands of
[02:25:16] exposed instances worldwide, this vulnerability poses a significant threat to organizations across all industries. The combination of widespread deployment, default insecure configurations, and the severity of the vulnerability creates an urgent need for immediate remediation. Organizations must prioritize updating their Redis instances and implementing proper security controls to protect against exploitation. This vulnerability
[02:25:45] also highlights how deeply today's cloud environments depend on open-source technologies like Redis. So, the biggest takeaway for our listeners is to check your own use in your organizations for any creaky older instances of Redis that might be running. You could simply perform an internal port scan for anything excepting TCP connections on
[02:26:14] port 6379. If any are found or known, carefully examine and consider who could obtain connections to its services. And of course, it's always best to keep current with open-source releases. In this instance, it could be crucially important. And if you've got any Redis in a cloud environment, make sure that it's not publicly exposed. It's just crazy. But for some reason, 330,000 instances are,
[02:26:44] which, again, you can't trust authentication. 60,000 don't have any need for that. But the other ones, yeah, who knows what the username and password is going to be. Wow. Well, I'm just going to trust that Patrick has locked our Redis instance down and is keeping it up to date. I think probably. If he's listening to this podcast, he listens
[02:27:14] religiously. In that case, I'm sure it's probably already been fixed, but if not, it will be. And the good news is, as far as I have seen, there's as yet no proof of concept. As soon as one gets published, then it's, you know, Katie bar the doors, I think, is an expression you and I have probably heard before. Once or twice. I don't know who Katie is. who Katie is, yeah. And whether it's the barn door, I don't know.
[02:27:45] You know, there's a lot of stuff written in Lua. It's a pretty cool language. Do you think this Lua interpreter flaw might hit other software? That's a good question, whether that's a shared exploit. Whatever it is, the problem in Lua escapes its own sandbox. Allowing external access. So, uh, that's, that's, I would imagine the whiz guys are on it if, uh, if they're, if
[02:28:14] it hadn't, uh, occurred to them. There's a ton of stuff coded in Lua. I really actually like it as a language, huh? Yeah. Okay. A lot of it's gaming. So, you know, so what if you have a use it? It's one of those hobby languages that sort of grew up. It's like PHP. Yeah. It's not as bad as PHP. It's not. I think it's a little better than PHP. Maybe not now that I know they've got this problem. Uh, okay. Ladies and gentlemen, that concludes this thrilling, gripping edition of security. Now we're getting better
[02:28:44] every episode and considering now this is our 1047th, we must be pretty darn good by now. They were getting the hang of it, getting the hang of it. Yeah. We do the show every Tuesday right after Mac Break Weekly. That ends up being around 1.30 Pacific, 4.30 Eastern, 20.30 UTC. We are still on summertime. We won't be on standard time until after Halloween because the candy makers want to make sure the kids get plenty of sunlight so they go out
[02:29:13] and get their candy. So for now, you can watch us live at those particular times in a number of places. If you're in the club, of course, in the club to a discord, that's the special access behind the velvet rope stuff. And if you're not in the club, join, please. It makes a big difference to us. It really helps us. And I think you get a lot of benefits, twit.tv slash club twit. But everybody can watch on YouTube, Twitch, x.com, Facebook, LinkedIn,
[02:29:44] and kick. So there's plenty of other places you can watch the show. You don't have to watch live. That's just for the hardcore folks who want the latest version, the freshest possible version of security now. The rest of you, of course, can get a copy on the website. We've got one at twit.tv slash sn. We've got two. We've got audio, 128 kilobit audio, which is more bits than you need, but that's how we do it. And there's video as well. Again, twit.tv slash sn. Steve has copies,
[02:30:14] unique copies at his website, grc.com. He's got a 16 kilobit audio. Okay, that's, just as we're too high, audio. Perfection. He also has very perfect transcripts written by an actual human, Elaine Ferris. Those are there. The show notes, he writes very complete show notes. They're wonderful. Actually, you can get those emails to you if you really want by
[02:30:44] going to grc.com slash email. The main purpose of the page is to whitelist your email address so you can send Steve pictures of the week and comments and so forth. But you'll notice there are two boxes unchecked by default below it. One is for his weekly Security Now newsletter with all the show notes. The other is for a very rare announcement newsletter. We're all waiting. We're all waiting for the announcement of DNS Benchmark Pro. Could be any day now.
[02:31:13] You'll get an email when that comes out. So that's how you stay in touch. Again, that's grc.com slash email. There are many, many other wonderful things to check out at GRC, including Steve's bread and butter. So it's very important to support Steve by buying a copy of Spinrite. If you have mass storage, and I know you do, then you need Spinrite. It's the world's best mass storage maintenance, performance enhancing, and recovery utility. That's at grc.com.
[02:31:42] We would like you to come back next Tuesday for this show. We will be here. I hope you will be. But in the meantime, I think it's time to say fond farewell. Hasta. Take care, Steve.